Why Your OT Security Pipeline Stays Empty — and How to Fix It
The OT security market is growing fast. Is your pipeline keeping up? Learn the outreach strategies that reach industrial buyers and close complex deals.

You’ve already run the email sequences. You’ve tried LinkedIn outreach. You may have even hired an SDR or two, briefed them on your ICS portfolio, and watched them struggle to get the right people on the phone.
Your OT security lead generation isn’t broken because you haven’t tried hard enough. It’s broken because the standard B2B playbook was never built for the structural complexity of industrial cybersecurity sales — and most vendors only figure that out after burning through budget and months of pipeline that never quite close.
This article is for OT and ICS security vendors who are past the awareness stage. You already know the market is growing. You know your solution is strong. What you need now is a clearer picture of why your current outreach model is underperforming, what a better-fit approach looks like, and whether outsourcing your OT security lead generation to a specialist partner is the right move for where your business is right now.
🧠 The Core Problem
Most OT security vendors don’t have a product problem or even a messaging problem. They have a go-to-market infrastructure problem: the wrong channels, incomplete buying committee coverage, and contact data that doesn’t reach the niche industrial roles that actually control OT security budgets. Fixing that infrastructure — not just tweaking copy — is what moves the needle.
The Numbers That Put This in Context
These aren’t abstract projections. They represent active buying pressure in your market right now — and a growing pool of industrial operators who are under real pressure to act. Most of your competitors are not reaching those buyers effectively. The vendors that move first with the right outreach model will claim the pipeline that everyone else is leaving on the table.
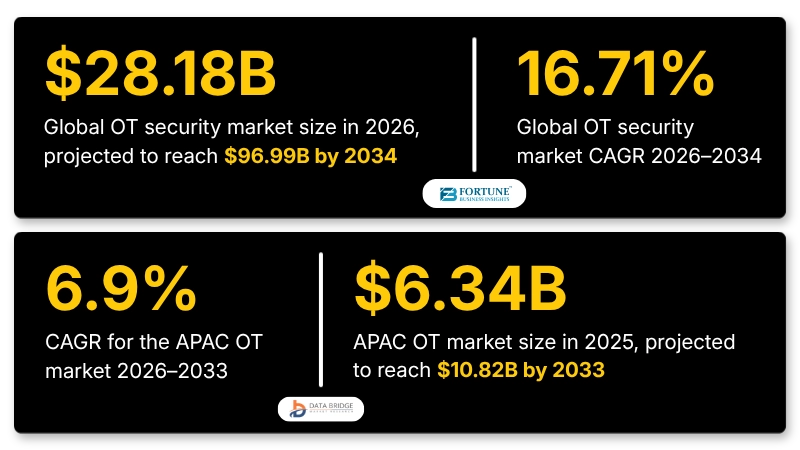
What makes these numbers particularly important for lead generation is the context behind them. The global OT market is being driven by a convergence of forces that are simultaneously creating urgency and complexity for buyers: accelerating industrial digitisation, IT/OT convergence exposing legacy systems to new threat vectors, tightening regulatory frameworks across every major region, and a growing realisation that the air-gap security model that protected industrial environments for decades no longer holds. Buyers are under pressure — and pressure creates a pipeline, if you know how to reach them.
Why OT Security Lead Generation Is Structurally Different
Most B2B lead generation advice assumes your buyer is digitally reachable. They’re on LinkedIn. They download whitepapers. They click on retargeting ads.
But OT security buyers are not “most” buyers.
The people who actually approve an ICS security investment — plant managers, automation engineers, operations directors — are often on the factory floor, not in their inbox. Standard digital channels simply don’t reach them. And even when you do reach them, you’re walking into a buying committee problem that most outreach models aren’t designed to handle.
A single OT security deal typically requires sign-off from the CISO (risk and compliance), the Plant or Operations Manager (uptime and continuity), and often Legal or Finance as well. These personas have different priorities, different vocabularies, and often entirely different views on what “risk” even means. Messaging that resonates with a CISO can completely miss with a plant manager — and if you’re only running one campaign track, you’re probably losing deals you don’t even know you had.
This complexity is compounded by a market-wide shift in governance. As OT security responsibility migrates upward toward the CISO level, the buying committee has become more IT-literate at the top — but the operational layer still reports to plant and engineering leadership. That structural tension means a deal can have executive sponsorship and still stall at the operational level if the plant manager hasn’t been brought into the conversation.
Long Sales Cycles and Cross-Functional Buying Committees
The average OT security deal takes 6 to 18 months to close. During that window, your prospect is consuming more than a dozen pieces of content, running internal risk assessments, fielding competing priorities, and managing day-to-day operational pressures. Keeping a qualified account engaged over that timeline — without being perceived as a nuisance follow-up — is genuinely hard.
Lead generation strategies that work for SaaS products, where a champion can push through approval quickly, don’t translate here. You need a nurturing model that maps to each stakeholder’s concerns and maintains momentum across a fragmented buying group.
The “Air Gap” Myth and Prospect Complacency
A significant portion of your target market genuinely believes they don’t need your solution yet. Many industrial operators still assume their systems are isolated from the internet. The reality — that modern vendor laptops, USB connections, and remote monitoring tools have quietly eliminated most of those gaps — hasn’t landed yet for a lot of plant-level decision-makers. Overcoming that complacency without resorting to fear-based messaging is one of the hardest things to get right in industrial cybersecurity outreach. Get it wrong, and you either fail to create urgency or you alienate the prospect entirely.
This isn’t a fringe problem. Data Bridge Market Research identifies growing cybersecurity risks across critical infrastructure as one of the primary restraints on OT market growth — not because the threat isn’t real, but because the Colonial Pipeline incident and similar high-profile attacks have created awareness at the executive level without necessarily changing behaviour at the operational level. Your outreach needs to bridge that gap. Overcoming complacency without resorting to fear-based messaging is one of the hardest things to get right in industrial cybersecurity outreach. Get it wrong, and you either fail to create urgency or you alienate the prospect entirely.
👀 Industry Insight
Regulation is increasingly doing the fear-reduction work for you. NERC CIP, NIS2, and IEC 62443 are driving active OT security procurement cycles in energy, utilities, and manufacturing. Vendors that align outreach to compliance timelines — rather than generic threat messaging — are seeing significantly higher response rates from their target accounts.
Understanding Your Buyer: CISOs, Plant Managers, and Compliance Officers
One of the most common and costly mistakes OT security vendors make is building their entire outreach strategy around a single persona. The CISO gets all the attention. But in most industrial environments, the CISO doesn’t have full authority over operational technology. The plant manager does, and they care about completely different outcomes.
The on-premise segment’s dominance — holding around 50% of the OT market in 2025 — tells you something important about your buyers’ mindset. They prioritise localised control, security, and compliance with industry-specific regulatory requirements. They want to maintain full control over sensitive operational data, reduce latency, and ensure system reliability in mission-critical applications. Your messaging needs to speak to that instinct for control and continuity, not just threat mitigation.
Here is what each stakeholder actually needs to hear:
- CISO / IT Security Leader: Risk reduction, compliance coverage (NERC CIP, NIS2, IEC 62443), integration with the existing security stack, and vendor credibility. They speak in threat models and frameworks. They want to know your solution fits their governance structure without creating new problems.
- Plant Manager / Operations Director: Uptime, production continuity, and whether your solution causes any disruption during deployment. They speak in equipment lifecycles and shift schedules. They are not interested in threat intelligence reports. They want to know you won’t slow the line.
- Compliance Officer / Legal: Regulatory alignment, audit readiness, and documentation. They want to know exactly what your solution covers, what it doesn’t, and whether it generates the kind of paper trail that protects them during an audit.
Effective ICS cybersecurity lead generation means running parallel outreach tracks — not one campaign that tries to speak to all three at once. Each persona needs a message tailored to their specific concern, delivered through a channel they actually use. This is not a nice-to-have. It is the difference between a deal that progresses and one that dies quietly in committee.
💡 Expert Tip
Map your outreach to the buying trigger, not just the persona. A plant manager who just experienced a near-miss incident is infinitely more receptive than one who hasn’t. Regulation-triggered accounts — those operating in sectors actively dealing with NERC CIP or NIS2 compliance deadlines — are often in an active buying window. Prioritise them in your account targeting and craft your opening message around the compliance pressure they’re already feeling.
5 Lead Generation Strategies for OT Security Vendors
Generic B2B outreach fails in this market. These are the approaches that consistently produce a qualified pipeline for industrial cybersecurity vendors.
1. Account-Based Outreach Targeting the Full Buying Committee
Instead of chasing individual leads, identify your highest-value target accounts and build multi-persona outreach sequences that engage the CISO and the plant manager simultaneously — with messaging tailored to each. This account-based marketing (ABM) approach prevents the most common OT security sales failure: one stakeholder is sold, and another quietly kills the deal.
ABM works especially well for high-value OT security deals because it mirrors how the actual purchase decision is made. You’re not convincing one person — you’re building consensus across a committee that may have never fully aligned before you started the conversation. With large enterprises dominating the OT market due to their extensive industrial operations and high investment capacity, ABM gives you the structured approach needed to navigate complex, multi-layered procurement processes at scale.
Most high-value industrial deals involve three or more decision-makers. If you want to see what persona-mapped ABM outreach looks like in practice, see how Callbox structures account-based campaigns for OT security vendors.
2. Regulation-Triggered Campaigns
NERC CIP, NIS2, and IEC 62443 are creating defined buying windows in energy, utilities, transportation, and manufacturing right now. Build campaign sequences that open with the specific compliance requirement your prospect is facing, connect it to the operational and financial consequences of non-compliance, and then position your solution as the path to both security and regulatory coverage.
This approach cuts through the “we’re already protected” objection because it shifts the frame from abstract threat scenarios to concrete legal and financial consequences — something both the CISO and the CFO understand and act on.
Compliance requirements and regulatory mandates are becoming more stringent globally as governments emphasise the protection of critical infrastructure, meaning these buying windows are not shrinking — they’re multiplying.
3. LinkedIn Outreach Done Right for Industrial Decision-Makers
LinkedIn remains the most reliable digital channel for reaching CISOs and IT security leaders in industrial sectors — but most vendors do it wrong. Generic connection requests followed by immediate product pitches are ignored. What works in 2026 is relevance-led engagement: commenting on industry discussions, sharing original insights on OT threats, and sending personalised messages that reference something specific about the prospect’s company, sector, or current regulatory environment.
For plant managers and operations leaders, LinkedIn is far less reliable. Phone outreach and structured calling programmes remain the most effective channel for reaching operational buyers who aren’t active on social platforms — as long as your callers are trained to speak their language and avoid making the cold calling mistakes that quietly kill your pipeline.
4. Intent-Signal Based Targeting
The best time to reach an OT security prospect is when they are already researching. Intent data tools track online behaviour — content consumption, search activity, competitor comparisons — and flag accounts that are actively evaluating solutions. Prioritising these accounts dramatically improves response rates because you’re reaching buyers who are already in a consideration mindset, not cold prospects who haven’t yet acknowledged the problem.
The growing adoption of Industrial IoT and AI-driven analytics is accelerating this signal activity. As organisations integrate SCADA, DCS, and PLC systems with cloud platforms and enterprise software, their research footprint expands — meaning more intent signals are available for vendors who know how to read them.
5. Webinars and Virtual Events Focused on Operational Risk
Industrial buyers attend events to learn, not to be sold to. A well-structured webinar on a topic like “Securing Legacy PLCs: What Changes After NIS2” positions your company as a credible expert and generates warm leads who have already raised their hand. Post-event follow-up sequences can then convert attendees into the pipeline with significantly less friction than cold outreach — because trust has already been established before the first sales conversation.
The SCADA segment is expected to witness the fastest growth in the OT market through 2033, driven by demand for centralised monitoring, real-time data visualisation, and predictive analytics. Webinar content that speaks directly to these priorities will resonate with the exact buyers who are actively evaluating solutions in the fastest-growing segment of your market.
💡 Expert Tip
Don’t limit event topics to threat intelligence. Topics that connect OT security to operational outcomes — production continuity, insurance premium reduction, audit compliance — attract plant managers and operations directors who typically skip traditional cybersecurity webinars. Mixing the audience is exactly what you need for multi-stakeholder deals.
In-House SDR Team vs. Outsourced Lead Generation for OT Security
Many vendors attempt to build an OT security pipeline in-house before eventually concluding that the cost and time investment isn’t sustainable. Here’s an honest comparison of both models.
| Factor | In-House SDR Team | Outsourced (e.g. Callbox) | Key Consideration |
| Ramp-Up Time | 3–6 months to hire, train, and build sequences | 2–4 weeks to campaign launch | Speed-to-pipeline is critical in long sales cycles |
| Persona Coverage | One SDR typically handles one persona track | Dedicated team covers CISO + OT buyer simultaneously | Multi-persona outreach is essential for OT deals |
| Data Quality | Depends on purchased lists; specialist roles hard to find | 35M+ verified B2B contacts, enriched for niche roles | 42% of B2B marketers cite poor data as the top barrier |
| Cost | $16,000+/month including tools, salary, overhead | From $6,667/month (6-month engagement) | In-house costs compound; outsourced scales flexibly |
| Control & Brand Voice | Full internal alignment with your messaging | Collaborative scripting; SDRs act as brand extension | Requires onboarding investment either way |
For most OT security vendors — especially those scaling into new markets or managing a lean sales team — the outsourced model offers a faster, more cost-efficient path to a qualified pipeline. The main advantage isn’t just cost. It’s having an experienced team that already knows how to reach industrial buyers and has the verified data infrastructure to support niche persona targeting from day one.
The SMB segment of the OT market is expected to grow fastest through 2033 as cost-effective and scalable OT solutions become more accessible. For vendors targeting this segment specifically, outsourced lead generation removes the overhead burden that makes in-house programmes unsustainable at smaller deal values and shorter engagement windows.
Weighing up in-house vs outsourced for your OT security pipeline?
Talk to a Callbox strategist and get a direct assessment based on your current setup — no obligation.
Entering or Scaling Into APAC? Here’s What OT Security Vendors Need to Know
The APAC OT market was valued at $6.34 billion in 2025 and is projected to reach $10.82 billion by 2033, growing at a CAGR of 6.9%. That sustained growth is being driven by a convergence of industrial automation investment, Industry 4.0 adoption, digital transformation across manufacturing and energy sectors, and deepening IT/OT integration across mission-critical infrastructure. For OT security vendors, this represents a long-duration pipeline opportunity — but one that requires a fundamentally different go-to-market approach than North American or European markets.
APAC is not a single market. It is a collection of distinct buying environments, each with its own regulatory framework, cultural norms, procurement process, and preferred communication channel. What works for a CISO in Singapore does not automatically work for a plant manager in Jakarta or a compliance officer in Tokyo. Vendors that treat APAC as a single outreach territory consistently underperform against those that localise their approach by market.
China: The Dominant Market You Can’t Ignore
China dominated the APAC OT market in 2025, driven by its vast industrial base, strong manufacturing ecosystem, and large-scale investments in smart factories and industrial automation. Government-backed programmes like Made in China 2025 have accelerated the deployment of SCADA, DCS, and PLC systems across utilities and manufacturing at a pace unmatched elsewhere in the region. The presence of major domestic automation providers and strategic collaborations with global industrial technology companies have created a highly competitive but high-volume opportunity for OT security vendors with the right localisation strategy.
Reaching Chinese industrial buyers requires Mandarin-language outreach, an understanding of domestic procurement preferences, and messaging that aligns with the government’s own industrial modernisation priorities. Generic English-language campaigns will not penetrate this market meaningfully.
Japan: Steady, Relationship-Driven Growth
Japan’s OT market is supported by its advanced manufacturing sector and early adoption of robotics and industrial automation. Japanese industries emphasise precision, reliability, and system integration — which accelerates deployment of PLC, DCS, and safety instrumented systems across automotive and electronics production. Strong regulatory standards and continuous modernisation of ageing infrastructure further support OT investments.
However, Japan is a deeply relationship-driven market. Vendor content in English alone is rarely sufficient to generate trust at the plant manager level. Outreach that demonstrates genuine understanding of Japanese industrial norms, combined with Japanese-language SDR capability, is the baseline requirement for meaningful pipeline development in this market.
Southeast Asia: Regulatory Pressure Creating Active Buying Windows
In Southeast Asia, government-mandated critical infrastructure protection programmes are pushing industrial operators to evaluate OT security solutions on defined timelines.
Singapore’s Operational Technology Cybersecurity Masterplan creates direct buying pressure for vendors serving energy, water, and transport sectors. Malaysia’s NACSA framework and Indonesia’s emerging BSSN regulations are creating similar windows in manufacturing and utilities.
The building and infrastructure segment is expected to witness the fastest growth through 2033, driven by smart building projects, IoT-enabled automation, and energy management initiatives — all of which expand the attack surface that OT security vendors are positioned to address.
Australia and New Zealand: Compliance-Triggered Buying Cycles
In Australia and New Zealand, the 2024 Security of Critical Infrastructure Act amendments extended mandatory cyber obligations to industrial sectors — creating a compliance-triggered buying cycle that mirrors what NERC CIP created in North America. ANZ manufacturing and resources companies are actively evaluating vendors right now, and the on-premise deployment preference that dominates the broader APAC market is particularly pronounced here, where data sovereignty and operational control are non-negotiable requirements.
What Effective APAC OT Security Lead Generation Requires
Multilingual outreach capability is non-negotiable in several key markets. Japanese, Bahasa Indonesia, Korean, and Mandarin-speaking SDRs are not a premium add-on — they are the baseline requirement for penetrating operational buyer personas who do not conduct business primarily in English.
Local regulatory fluency matters as much as product knowledge. Your outreach needs to reference the compliance frameworks your APAC prospects are actually facing — not the North American or European frameworks you’ve built your messaging around. An outreach message that opens with NERC CIP will not resonate with a Singapore energy operator navigating the OT Cybersecurity Masterplan.
Time zone alignment affects pipeline velocity more than most vendors acknowledge. APAC deals managed from a North American or European timezone consistently see longer response cycles, slower meeting progression, and higher drop-off rates at the proposal stage. Having SDR coverage aligned to APAC business hours is not a logistics detail — it is a conversion factor.
Callbox’s Singapore and Malaysia offices, combined with multilingual SDR teams covering Southeast Asia, ANZ, Japan, and South Korea, give OT security vendors a credibility and coverage advantage that globally-focused competitors without regional presence cannot easily replicate. For vendors entering APAC for the first time or scaling beyond an initial market, this regional infrastructure removes months of setup time and eliminates the most common APAC pipeline failure modes.
Looking to build an OT security pipeline in APAC?
See how Callbox supports vendors entering and scaling across Southeast Asia and ANZ.
How Callbox Generates Qualified Leads for OT and ICS Security Vendors
With over 20 years of B2B go-to-market experience and a database of more than 35 million verified contacts, Callbox is built for exactly the kind of complex, high-value industrial deals that define the OT security market. The approach is not a generic outreach campaign dropped onto a new industry. It’s a structured, account-based program designed around the specific buying dynamics of industrial cybersecurity.
Multi-Touch, Multi-Persona Outreach Across Every Relevant Channel
Callbox’s Smart Engage platform runs coordinated outreach sequences across email, phone, LinkedIn, content syndication, and events — reaching the full buying committee simultaneously. A Plant Manager gets a call that speaks their language. A CISO gets a LinkedIn message referencing the compliance requirement their sector is actively dealing with. Each touchpoint is tracked and sequenced so no stakeholder falls through the cracks over a 6-to-18-month sales cycle.
OT-Specific Data Enrichment
Finding “ICS Security Architect” or “Automation Engineer” on a generic contact list is next to impossible. Callbox’s 300-person data team maintains human-verified contact records filterable by firmographics that matter for OT security: industry vertical, manufacturing capacity, legacy system environment, and technology stack. This is what eliminates the wasted outreach that comes from targeting the wrong contacts.
OT Security Leader Drives APAC Pipeline in 3-Month Programme
An APAC-based industrial automation and OT security provider needed a structured outbound program to reach enterprise manufacturers and critical infrastructure operators across the region. In three months, Callbox delivered 34 Sales Qualified Leads, 72 Marketing Qualified Leads, 41 webinar registrations, and an 8% no-show rate through a targeted, multi-channel ABM program.
READ CASE STUDYHow to Measure ROI on OT Security Lead Generation
- Define Your Average Deal Value: OT security contracts typically range from $50K to $500K+, depending on scope. Establish a conservative average deal value to use as your baseline for ROI calculations.
- Set a Realistic Appointment-to-Close Rate: For complex industrial sales, a 20–30% close rate from qualified meetings is a reasonable benchmark. Work backwards from your target revenue to set appointment volume goals.
- Track Pipeline Velocity, Not Just Volume: The goal of a specialist lead generation partner isn’t just more leads — it’s shorter time-to-close. Track how quickly appointments progress to proposals and proposals to contracts.
- Measure Cost Per Qualified Meeting: Divide total monthly investment by the number of qualified meetings booked. For Callbox engagements, clients consistently see this metric improve as campaigns mature and messaging is refined.
- Apply the Revenue Math: Example: 50 leads × 30% conversion to opportunities × 20% close rate × $75K deal value = $225K revenue from a $10K–$23K monthly investment. That’s a measurable, repeatable pipeline engine.
OT Security Lead Generation: Frequently Asked Questions
What makes OT security lead generation harder than standard B2B lead generation?
OT security requires reaching buyers who are often offline, navigating buying committees with conflicting priorities, managing 6-to-18-month sales cycles, and overcoming genuine complacency in a market where many prospects still believe their systems are adequately protected. The convergence of IT and OT systems is expanding the attack surface faster than most industrial operators realise — but awareness at the plant level still significantly lags awareness at the CISO level. Generic B2B tactics don’t account for any of these factors.
Who makes OT security purchasing decisions — the CISO or the plant manager?
Both, and often more stakeholders as well. The CISO typically owns risk and compliance decisions. The Plant or Operations Manager owns uptime and system continuity. Legal and Compliance may also be involved. With 52% of organisations now placing OT security under the CISO — up from 16% in 2022 — the governance structure is shifting, but the operational sign-off requirement at the plant level remains. Effective outreach must address all three personas with tailored messaging simultaneously — not sequentially.
How can OT security vendors generate leads from compliance-driven buyers?
Build campaigns around specific compliance deadlines — NERC CIP audit cycles, NIS2 implementation timelines, or IEC 62443 certification requirements. Compliance requirements and regulatory mandates are becoming more stringent globally as governments emphasise the protection of critical infrastructure. Prospects already under regulatory pressure are in active evaluation mode and respond significantly better to outreach than cold accounts with no immediate compliance driver.
How long does it take to see results from outsourced OT security lead generation?
With a specialist partner like Callbox, most campaigns begin producing qualified meetings within the first 4 to 6 weeks. Pipeline acceleration — where the sales cycle begins to shorten as messaging is refined — typically becomes visible within the first 60 to 90 days.
Is outsourced lead generation effective for OT security vendors in the APAC market?
Especially in APAC, where local market knowledge and multilingual outreach capability are not optional extras — they are conversion requirements. The APAC OT market is growing steadily at 6.9% CAGR through 2033, with China dominating and India projected to be the fastest-growing country in the region. Callbox’s Singapore and Malaysia offices cover Southeast Asian industrial markets with a regional credibility advantage that globally-focused competitors without local presence simply cannot replicate.



